Edge Computing Architecture : A Complete Guide
Edge computing architecture is a current method of distributed computing that is closer to data sources. In addition, it reduces latency by processing information closer to users and devices. Thus, this can address real-time applications that require quick response. Also, edge architecture increases efficiency through the reduction of redundant data transmission. In this article, we […]
Hybrid Cloud Management: Flexibility and Efficiency in Modern IT

Modern organizations face constant pressure to innovate while maintaining efficiency in a rapidly changing digital world. Hybrid cloud management has become one of the revolutionary solutions. Hybrid clouds combine both the advantages of the private and public clouds. This assists organizations in being more flexible, scalable, and cost-saving. So, they are also known to guarantee […]
A Guide to Energy Efficient Computing
Computing has been a concern where organizations seek smarter technology usage. Performance is important; however, minimization of power consumption has taken over as well. The new generation demands machines that are fast and efficient at reducing energy expenses. Due to this move, most industries are currently seeking alternative strategies that can enable them to achieve […]
ML Model Deployment: Guide to Bringing Models into Production

Machine learning or ML model deployment refers to the action of implementing training in practice. It also fills the gap between experimentation and implementation so that predictive models can be useful. This phase involves the organizations incorporating models into the production systems, which enable them to produce insights, automate processes, and enhance real-time decision-making. The […]
Infrastructure as Code Platforms: Simplifying IT Management
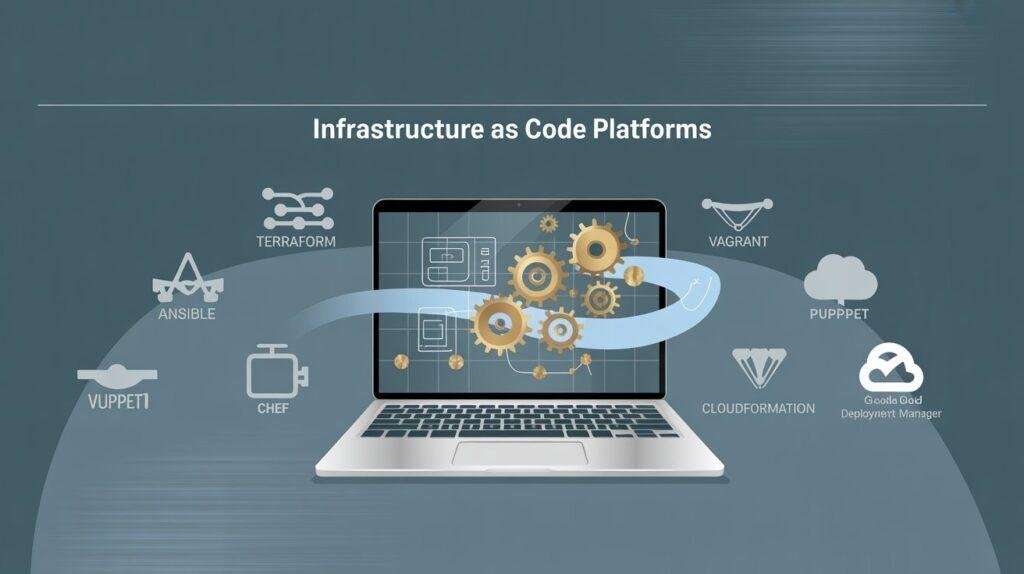
Technology is evolving rapidly, and associations need dependable ways to manage complex systems. Infrastructure as Code platforms offer that trustworthiness. They help teams replace homemade setups with automated, harmonious environments. This shift reduces errors and saves time. Importantly, it also helps businesses scale quickly. Through automation, these platforms allow inventors to concentrate on invention rather […]
Infrastructure as Code: A Complete Professional Guide
The way IT is structured has changed a lot in recent times. In the story, brigades had to configure waiters manually. This was slow, repetitious, and prone to crime. With business needs growing rapidly, companies started looking for quicker and smarter styles. That’s where infrastructure-as-code has come, the ultramodern approach. This article offers infrastructure as […]
Converged Infrastructure: A Complete Guide
In the current rapid digital landscape, companies are always looking for methods to streamline their IT processes while enhancing efficiency. This is where converged infrastructure becomes relevant. A converged infrastructure combines servers, storehouse, and networking into one optimized system rather than handling them singly. This integration streamlines operations, reduces costs, and improves the effectiveness of […]
Deep Sea AI Data Center Revolution: Exploring the Future

Modern technology demands smarter, sustainable infrastructure. A groundbreaking solution is emerging: the deep sea AI revolution. With the rise of data center artificial intelligence, industries are exploring uncharted territories—literally. The deep sea data center concept promises performance, efficiency, and environmental sustainability. Also, with the digital world growing fleetly, the need for strong computing is rising […]
Data Center as a Service (DCaaS)

The Data Center as a Service is being adopted by organizations in the modern digital landscape. It helps them manage data storage and IT needs easily. With a subscription model, DCaaS saves companies from paying large upfront costs. Furthermore, providers handle everything from hardware and software to networking and security, making it a more convenient […]
Data Center Services

Data center services are vital for global businesses, governments, and organizations in a digital era. They furnish secure and efficient storage and management solutions for data volumes that grow exponentially. In ensuring the effective management of data within today’s digital landscape, these services prove indispensable. Moreover, from consulting to cleaning, they encompass various functions critical […]

