How does AI in Cybersecurity works?
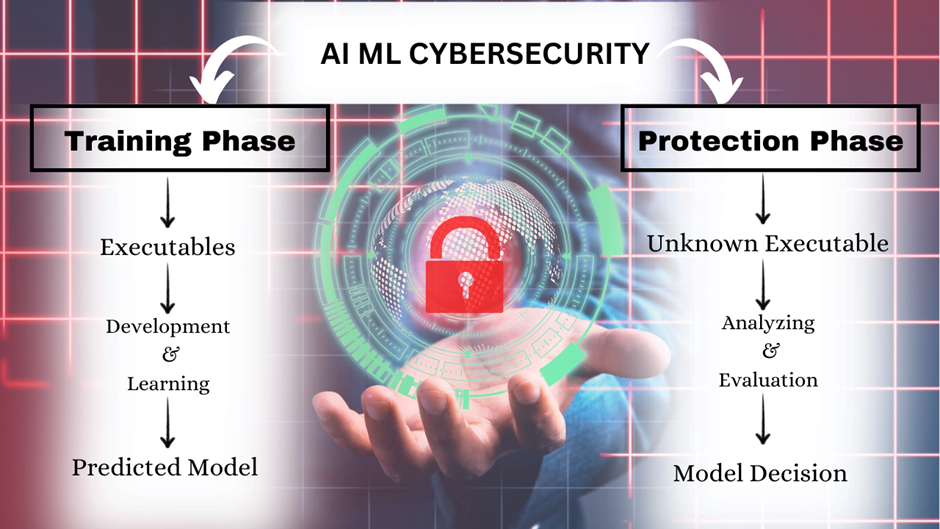
How does AI in Cybersecurity works? Uncategorized September 17, 2023 AI in cybersecurity is the cutting-edge fusion of artificial intelligence and security measures, fortifying digital landscapes against ever-evolving threats. Organizations gain the upper hand in detecting and thwarting malicious activities in real time by employing AI cybersecurity solutions. This technology excels at behavioral analysis, identifying […]
How Deception Technology Helps Organizations Detect Threats?
Imagine hackers stepping into a trap without realizing it. Deception technology uses realistic decoys to lure attackers, giving security teams instant alerts and a chance to stop threats before they reach critical systems. Additionally, Deception technology enhances visibility of threats by revealing bad practices at an initial stage of interaction within the networks. Moreover, the […]
Risks of Agentic AI: The Dark Side of Agentic AI

AI is still revolutionizing industries and providing efficiency and automation. However, it is impossible to disregard the risk of agentic AI. These AIs are not controlled by humans as they make decisions without supervision. Although all the potential advantages are enormous, including increased productivity and accuracy in operations, organizations should balance them with the risks […]
Cipher Feedback Explained: A Guide to CFB Mode
Block ciphers serve as the foundation of secure communication in synchronous cryptography. Nonetheless, block ciphers on their own aren’t always suitable for handling streaming data. To tackle this issue, cryptographers developed specialized operating modes. A generally used method is cipher feedback, also known as CFB. It provides a secure system for cracking data channels of […]
Cognitive Automation: The Future of Smart Workflows
In the present speedily-paced world, businesses are always seeking ways to enhance effectiveness, delicacy, and productivity. That’s where cognitive automation comes in. Unlike traditional automation, which follows predefined rules, cognitive systems use AI and ML to dissect data and make opinions continuously over time. This advanced technology is revolutionizing diligence by reducing homemade workloads, perfecting […]
DeepSeek AI introduces Deepseek R1

In today’s world, artificial intelligence is changing lives, work, and innovation profoundly. Among these pioneers, DeepSeek AI stands out with transformative solutions. It offers innovative tools for software development, solving problems, and automating processes efficiently. Moreover, DeepSeek AI simplifies complex challenges by enhancing productivity through technology. This revolutionary platform bridges automation and creativity seamlessly. Therefore, […]
Agents in AI
AI has made remarkable progress in a short time. Among its innovations, agents in AI play a vital role. They help automate tasks and solve complex problems efficiently. These systems observe their surroundings, make decisions, and take appropriate actions. This article will explain what agents in AI are. Then, we will explore their architecture. Finally, […]
Neural Interface by Meta for Next-Gen Orion AR Glasses
In the ever-evolving world of meta wearables, Meta has now taken a monumental leap forward with its development. Moreover, they have created cutting-edge neural technology for their next-generation Orion AR glasses, further enhancing user experiences. This breakthrough is a key step in blending neuromodulation technology at the neural interface, enhancing human-computer interaction. These advancements position […]
OWASP Top Ten

The OWASP Top Ten is important for steering your organization toward secure coding. This allows developers to prioritize and address these issues effectively. Following OWASP guidelines helps organizations improve security and meet industry standards. Using these best practices is crucial for strong cybersecurity. Consequently, it helps protect against common vulnerabilities and ensures the development of […]
Vulnerability Assessment
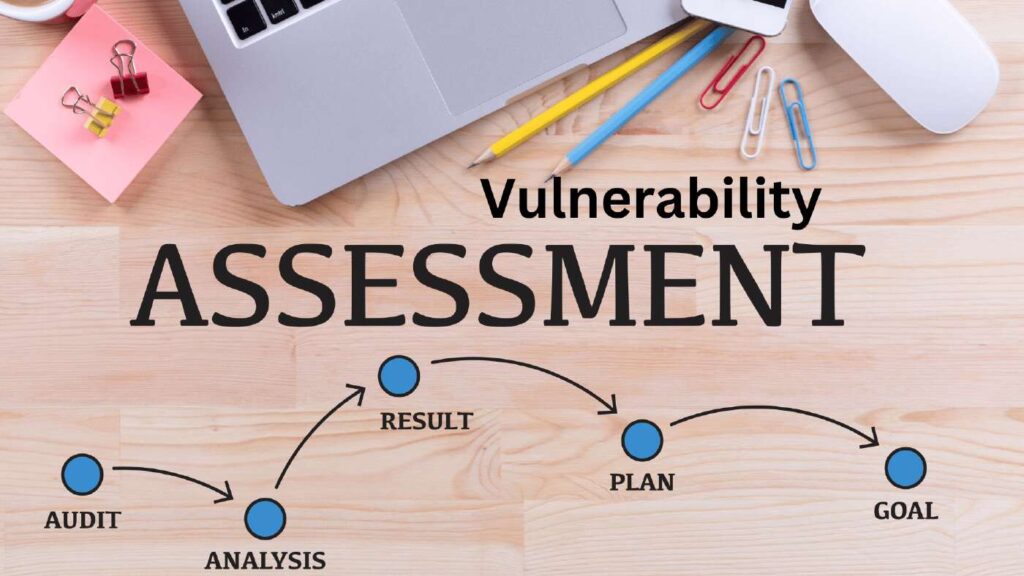
As cyber adversaries adapt tactics, the Vulnerability Assessment is a vital defense, safeguarding digital infrastructure. It promptly identifies and addresses security vulnerabilities. It promptly identifies and addresses security vulnerabilities. Furthermore, safeguarding systems and data is vital in today’s digital landscape. Additionally, as cyber threats evolve rapidly, organizations encounter heightened susceptibility to breaches. Therefore, robust cybersecurity […]

